Why Is the Indian Power Sector Vulnerable to Malware-Based Attacks?
Imagine this: it is a hot summer evening in Delhi, and suddenly, the lights go out. Fans stop spinning, air conditioners fall silent, and traffic signals freeze. Hospitals switch to backup generators, trains halt, and millions are left in darkness. This is not just a possibility; it has happened before. In July 2020, a massive blackout hit Mumbai, affecting over 2.5 million people. While the official cause was a grid failure, whispers in cybersecurity circles pointed to something more sinister: a malware attack. India’s power sector, the backbone of its growing economy, is increasingly under threat from malware-based cyber attacks. With over 1.4 billion people relying on electricity for daily life, healthcare, education, and industry, the stakes could not be higher. In this blog post, we will explore why India’s power infrastructure is so vulnerable to malware, how these attacks happen, and what can be done to protect it. We will keep things simple, clear, and actionable, so even if you are new to cybersecurity, you will understand the risks and solutions.

Table of Contents
- Overview of India’s Power Sector
- What Is Malware and How Does It Threaten Power Systems?
- Key Vulnerabilities in Indian Power Infrastructure
- How Malware Enters Indian Power Systems
- Real Incidents and Close Calls in India
- How India Compares to Other Countries
- Steps to Strengthen India’s Power Sector
- Conclusion
Overview of India’s Power Sector
India is the third-largest producer and consumer of electricity in the world. As of 2025, the country has an installed capacity of over 450 gigawatts (GW), with coal, renewable energy, and hydropower leading the mix. The power grid is divided into five regional grids: Northern, Eastern, Western, Southern, and North-Eastern, all synchronized under the National Grid. State-owned companies like Power Grid Corporation of India Limited (PGCIL), NTPC, and various State Electricity Boards manage generation, transmission, and distribution.
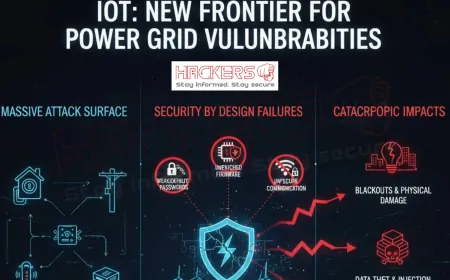
The sector has modernized rapidly. Smart meters, SCADA systems (Supervisory Control and Data Acquisition), and IoT devices now monitor and control power flow. Remote access allows engineers to manage substations from control rooms hundreds of kilometers away. While this improves efficiency, it also creates digital entry points for attackers.
What Is Malware and How Does It Threaten Power Systems?
Malware is short for “malicious software.” It is code designed to harm, steal, or control a system without the user’s knowledge. In the context of power grids, malware can do the following:
- Shut down generators
- Open circuit breakers to cause blackouts
- Alter voltage levels to damage equipment
- Encrypt critical files and demand ransom (ransomware)
- Spy on operations for future attacks
Unlike traditional IT systems, power systems use Operational Technology (OT). OT controls physical processes. A malware attack on OT can cause real-world damage: fires, explosions, or long-term blackouts.
Key Vulnerabilities in Indian Power Infrastructure
India’s power sector faces unique challenges that make it prone to malware attacks.
Legacy Systems Still in Use
Many SCADA systems and Remote Terminal Units (RTUs) were installed in the 1990s and early 2000s. These run on old operating systems like Windows XP or custom firmware that no longer receive security updates. Patching them is risky because downtime affects millions of users.
Lack of Network Segmentation
In many utilities, the corporate IT network (used for emails and billing) is connected to the OT network (used for controlling substations). A breach in the IT side can easily spread to critical controls.
Weak Remote Access Security
Engineers use Virtual Private Networks (VPNs) or dial-up modems to access systems remotely. Many use default passwords like “admin” or “1234”. Some systems allow direct internet access without multi-factor authentication (MFA).
Dependence on Third-Party Vendors
Power companies rely on vendors for hardware, software, and maintenance. A single compromised vendor can infect hundreds of utilities through software updates or support tools.
Limited Cybersecurity Awareness
Field technicians and plant operators often lack training in cyber hygiene. They may plug in personal USB drives or click on phishing emails, unknowingly introducing malware.
Underfunded Cybersecurity Teams
While IT budgets are growing, cybersecurity in OT remains underprioritized. Many state utilities have no dedicated cyber response team.
How Malware Enters Indian Power Systems
Malware does not appear out of thin air. It needs a way in. Here are the most common entry points:
- Phishing Emails: Fake emails from “suppliers” or “management” trick employees into downloading infected files.
- Compromised Software Updates: Hackers breach a vendor’s update server and push malware-laced patches.
- USB Drives: Infected pen drives used by contractors spread worms like Stuxnet.
- Exposed Devices: Substations with internet-facing SCADA interfaces are found using tools like Shodan.
- Insider Threats: Disgruntled employees or bribed staff install malware intentionally.
- Watering Hole Attacks: Hackers compromise websites frequented by power engineers and inject malware.
Real Incidents and Close Calls in India
India has faced several malware-related incidents in its power and critical infrastructure.
| Year | Incident | Target | Impact |
|---|---|---|---|
| 2020 | Mumbai Grid Failure | Tata Power | 2.5 million affected; suspected cyber component |
| 2021 | Ladakh Blackout | Military & civilian grid | Attributed to Chinese malware probe |
| 2022 | Ransomware on State DISCOM | Uttar Pradesh Power Corp | Billing systems locked; operations disrupted |
| 2023 | Phishing Campaign | Multiple utilities | Credentials stolen; no blackout but high risk |
In February 2021, Recorded Future reported that Chinese state-sponsored hackers targeted Indian power grids near the Ladakh border with malware. While no blackout occurred, the intent was clear: to gain control during geopolitical tensions.
How India Compares to Other Countries
India is not alone, but its challenges are unique.
- Ukraine (2015–2016): First confirmed malware-induced blackouts. India has similar legacy SCADA but less segmentation.
- USA: Strong regulations (NERC CIP), but ransomware still hits utilities. India lacks mandatory OT cybersecurity standards.
- China: Heavy investment in grid cyber defense. India is catching up but lags in funding and talent.
Steps to Strengthen India’s Power Sector
Protecting the grid requires action at multiple levels.
Technical Measures
- Segment IT and OT networks with firewalls
- Replace or isolate legacy systems
- Enforce multi-factor authentication (MFA)
- Monitor SCADA traffic for anomalies
- Use endpoint detection on all devices
Policy and Regulation
- Make CERT-In guidelines mandatory for utilities
- Enforce regular cyber audits
- Create a National Grid Cyber Emergency Response Team
Training and Awareness
- Train all staff on phishing and USB safety
- Run simulated cyber attack drills
- Partner with academia for OT cybersecurity talent
Vendor Security
- Audit third-party software before deployment
- Require secure-by-design updates
- Limit vendor remote access
Conclusion
India’s power sector is the lifeline of its economy and society. Yet, it remains dangerously vulnerable to malware-based attacks due to legacy systems, poor segmentation, weak remote access controls, and limited cybersecurity investment. Real incidents, from Mumbai’s blackout to Chinese probing in Ladakh, show that the threat is not theoretical. Malware can enter through phishing, USBs, or compromised updates, and once inside, it can cause devastation. But there is hope. With strong segmentation, regular training, mandatory standards, and government support, India can build a resilient grid. The time to act is now, before the next attack leaves millions in the dark. A secure power sector is not just about technology; it is about national security, economic stability, and public safety.
What is malware in the context of power grids?
Malware is harmful software that can control, damage, or spy on power systems. It can open breakers, encrypt data, or cause blackouts.
Has India ever had a malware-induced blackout?
Not confirmed officially, but the 2020 Mumbai blackout and 2021 Ladakh incident had strong cyber indicators.
Why are old SCADA systems risky?
They run on outdated software with known flaws and no security updates. Patching them risks downtime.
What is network segmentation?
It means separating office IT networks from control system networks so a breach in one does not spread.
How does phishing affect power companies?
Employees click fake emails, download malware, and give hackers a foothold into critical systems.
Can USB drives infect power grids?
Yes. Infected USBs used by staff or contractors can spread malware, even in air-gapped systems.
Who is targeting India’s power sector?
State-sponsored groups from neighboring countries and ransomware gangs seeking profit.
Are smart meters a cyber risk?
Yes, if poorly secured. Millions of internet-connected meters can be hacked to disrupt billing or demand.
What is ransomware in utilities?
Malware that locks systems or data and demands payment. Some Indian DISCOMs have been hit.
Does India have cybersecurity rules for power?
Yes, CERT-In guidelines exist, but they are not mandatory for all utilities.
Can AI help detect malware in grids?
Yes. AI monitors SCADA traffic and flags unusual patterns faster than humans.
Why is vendor security important?
Hackers often breach vendors to push malware through software updates to many utilities.
What is an air-gapped system?
A system with no internet connection. But even these can be infected via USB or insider access.
How can employees help prevent attacks?
Avoid suspicious links, never use personal USBs, report odd system behavior, and follow training.
Is 5G a risk to power grids?
Yes, if used without encryption. It expands connectivity and thus the attack surface.
What is a zero-day attack?
An attack using a software flaw unknown to the vendor. No patch exists yet.
Can solar inverters be hacked?
Yes. Many are internet-connected and run vulnerable firmware. Hackers can turn off solar output.
Who should fund grid cybersecurity?
Government, utilities, and consumers through regulated tariffs. It is a shared responsibility.
Will India face more grid attacks in the future?
Yes, as digitalization grows and geopolitical tensions rise, attacks will increase in frequency and sophistication.
How can India prepare for a major cyber blackout?
Build backup control centers, train rapid response teams, stock spare parts, and practice recovery drills.
What's Your Reaction?